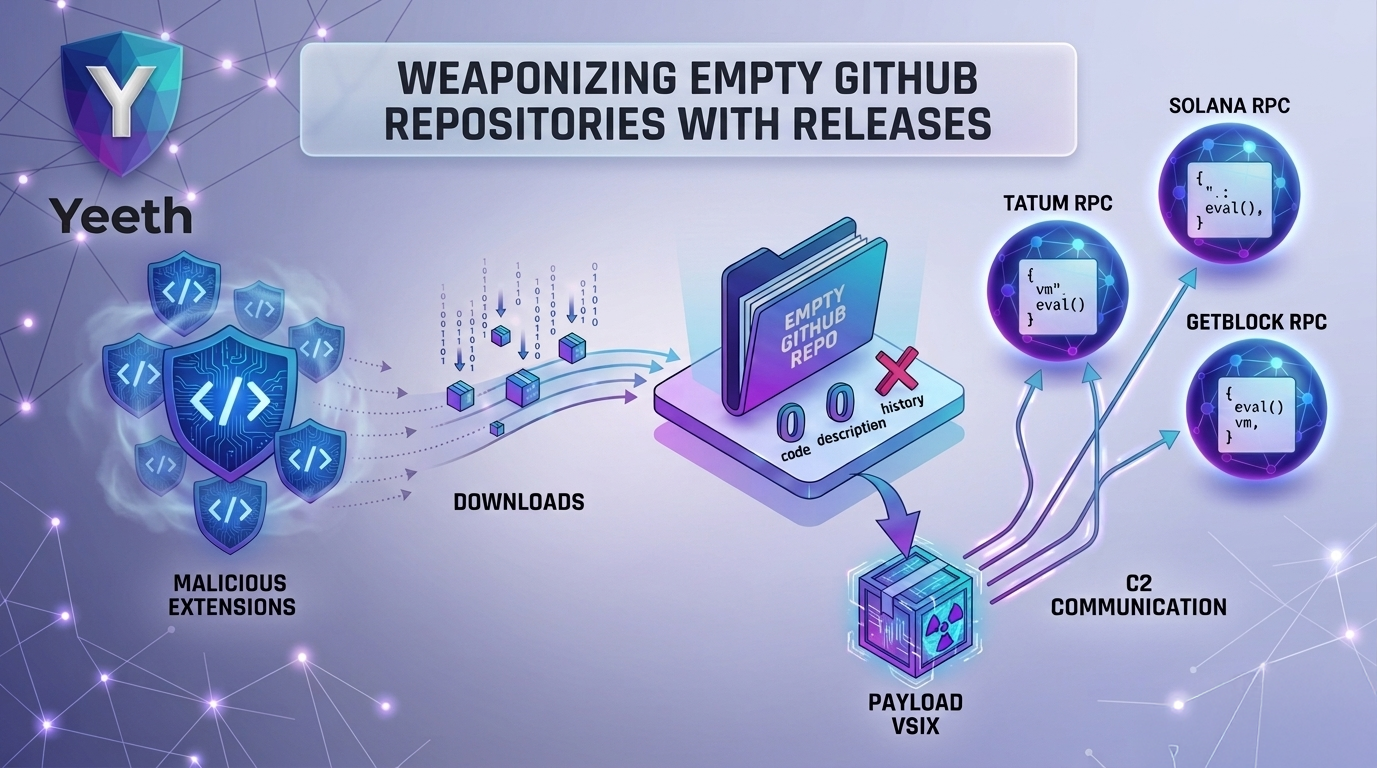
We’ve been tracking a cluster of VS Code extensions that all do the same thing on activation: reach out to github.com/francesca898/dqwffqw/releases. The repository has no code, no description, and no commit history. It exists to only host one release.
The Droppers
The first extension we caught, named catspace-studio.ng-angular-language-21.1.3, was advertised as an Angular language services extension. The legitimate Angular tooling is real and the extension wraps a functional language client. Packaged alongside it are native binaries for both Windows (extension/bin/win.node) and macOS (extension/bin/mac.node).
On activation, the entry point loads whichever binary fits the host platform and calls install(). That function reaches out to the francesca898/dqwffqw release page, fetches the payload, and notably also runs --install-extension to install additional extensions through the IDE’s own CLI. The dropper can silently expand its own footprint by installing further extensions the attacker controls, taking its functionality beyond just downloading a payload. Argus assigned this extension a risk score of 87/100.
A second dropper, sxatvo-tm.compile-runnner-build-1.0.91, follows the same pattern. It presents as a C/C++ compile-run helper and ships a Windows-only binary at dist/bin/win.node. Same delivery URL, same install() pattern. Argus assigned this extension a risk score of 85/100.
Both binaries contain matching strings: WinHTTP API calls, process creation functions, the francesca898/dqwffqw release URL, and IDE command-line paths. Neither does anything related to the features the extension claims to provide.
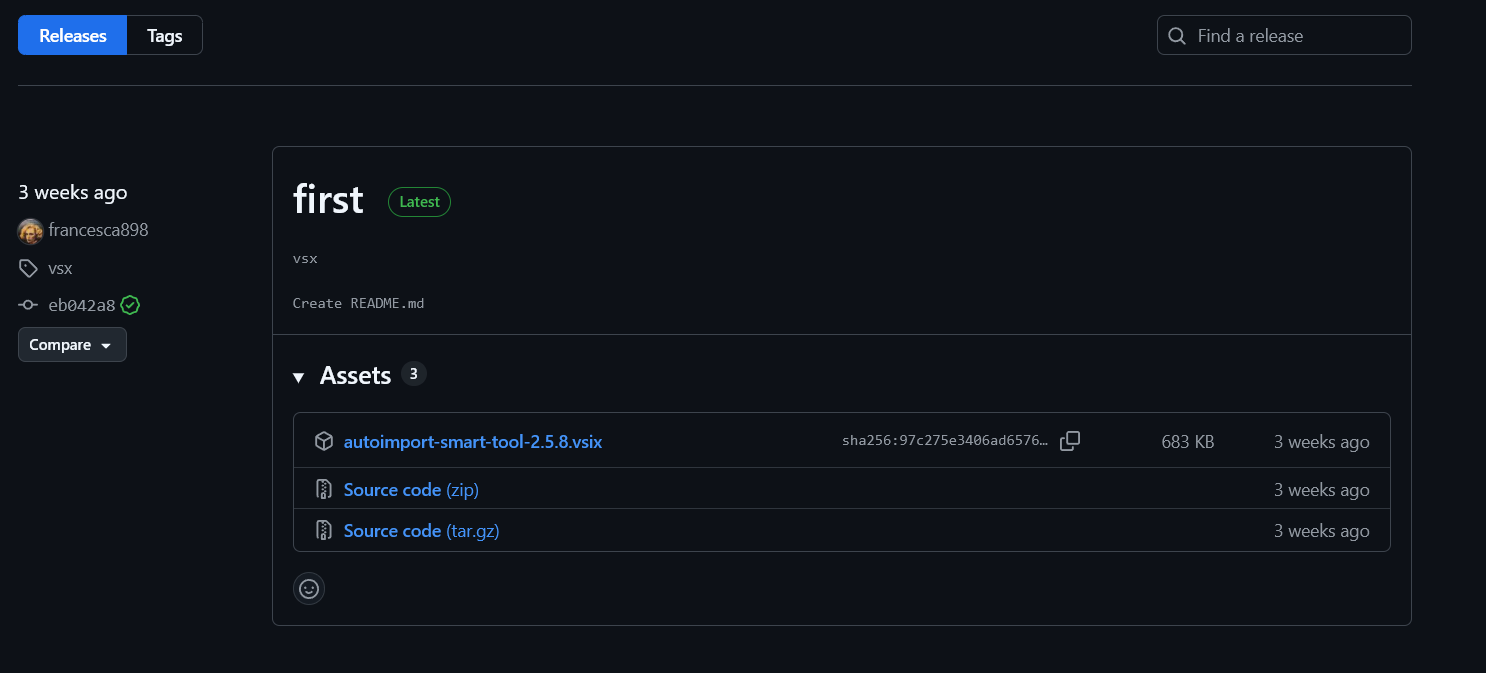
francesca898/dqwffqw — autoimport-smart-tool-2.5.8.vsix is the malicious payload fetched by both dropper extensions on activation.The Payload
The downloaded extension is autoimport-smart-tool-2.5.8. Argus assigned this extension a risk score of 90/100. The extension is separately listed on VirusTotal as well.
The bundle is heavily obfuscated. Inside out/src/extension.js, a loop builds a list of remote URLs — blockchain RPC endpoints from services like Solana, Tatum, and GetBlock — and begins making requests to them on startup. When responses come back, it decodes and executes the contents via eval(atob(...)) or Node’s vm module. It also reads system information (OS platform, hostname) and writes data to disk.
The extension claims to handle TypeScript and JavaScript auto-imports.
Why Blockchain RPCs?
Domain blocklists can’t touch Solana RPC endpoints without collateral damage. Blocking solana-rpc.p...com or getblock.io breaks legitimate crypto developer tooling. The attacker encodes commands in JSON-RPC responses, decodes them client-side, and executes them locally — a C2 channel that survives most network filtering by blending in with traffic that defenders have explicitly chosen not to block.
Developer machines are a good target for this technique specifically because they’re more likely to have crypto tooling installed and those network paths already open.
The Delivery Chain
Victim installs dropper extension (catspace-studio or sxatvo-tm)
→ activation loads platform-specific native binary
→ binary calls install()
→ fetches payload from github.com/francesca898/dqwffqw/releases
→ optionally installs additional extensions via --install-extension
→ payload runs, connects to blockchain RPCs
→ executes arbitrary remote code via eval/vm
The droppers share no publisher name and no code in common. What links them is a single URL. We expect more extensions using the same delivery mechanism — the pattern is simple enough to replicate across any number of publisher accounts.
Context
This campaign follows a pattern we’ve seen evolve over several months. GhostDrop pre-positioned 174 accounts for future payload delivery. PackRAT used extensionPack chaining to funnel installs toward malicious extensions. This campaign skips the registry entirely for the payload — the droppers land in the marketplace, but the malicious code lives on GitHub and never gets scanned.
That split is deliberate. Marketplace scanners look at what’s published. If the published extension looks clean enough, it passes. The payload arrives post-install from an external host, under the permissions the IDE already granted.
Using a GitHub release page as the payload host is low-friction. No infrastructure to maintain, no domain to register. GitHub’s CDN handles the distribution. The francesca898 account was likely created specifically for this campaign.
Conclusion & Remediation
All extensions listed below have been removed from the marketplace. If you have any of them installed, uninstall immediately and audit for persistence — the payload writes to disk and reads system information on activation. The --install-extension behavior in the catspace dropper means other malicious extensions may have been silently installed alongside it.
If francesca898/dqwffqw appears in any network logs, treat it as active compromise.
The dev-guard extension detects dropper behavior and suspicious activation patterns. Keep it updated as we continue tracking this campaign.
Indicators of Compromise (IOCs)
Delivery Infrastructure
- GitHub account:
francesca898 - Payload repository:
https://github.com/francesca898/dqwffqw - Payload release URL:
https://github[.]com/francesca898/dqwffqw/releases/download/vsx/autoimport-smart-tool-2.5.8.vsix
Payload
- Extension:
autoimport-smart-tool-2.5.8.vsix - File hash (SHA-256):
97c275e3406ad6576529f41604ad138c5bdc4297d195bf61b049e14f6b30adfd
Network Indicators
- Blockchain RPC endpoints (Solana, Tatum, GetBlock) used as C2 channel
francesca898GitHub account: any outbound connection should be treated as malicious
Read More
All Posts → Threat Intel
Threat Intel
The Malware Factory: GLASSWORM Forensics in Open VSX
Sixteen extensions in 48 hours. All share one author. A forensic walkthrough of how Bane, Yeeth Security's threat-int...
 Threat Intel
Threat Intel
 Threat Intel
Threat Intel
Weaponizing Extension Packs with PackRAT
Dissecting a Downloader Abusing Extension Packs for Stealthy Distribution